
by dlstrom-sds | Jun 4, 2024 | resources
Of course you do! And let’s talk about why. So the real question becomes two — Why is this important? and How do you do this? Let’s work on answering the first question… Why is a cybersecurity risk assessment important for your organization? Think of the...

by dlstrom-sds | May 19, 2024 | resources
Think about this possibility… It’s Monday morning. You’re dragging and you head to the coffee pot to get the first cup of the day. People are just starting to show up at the office. Then you hear a loud BOOM, the electricity goes off and the alarms go off....
by dlstrom-sds | Jul 17, 2023 | resources
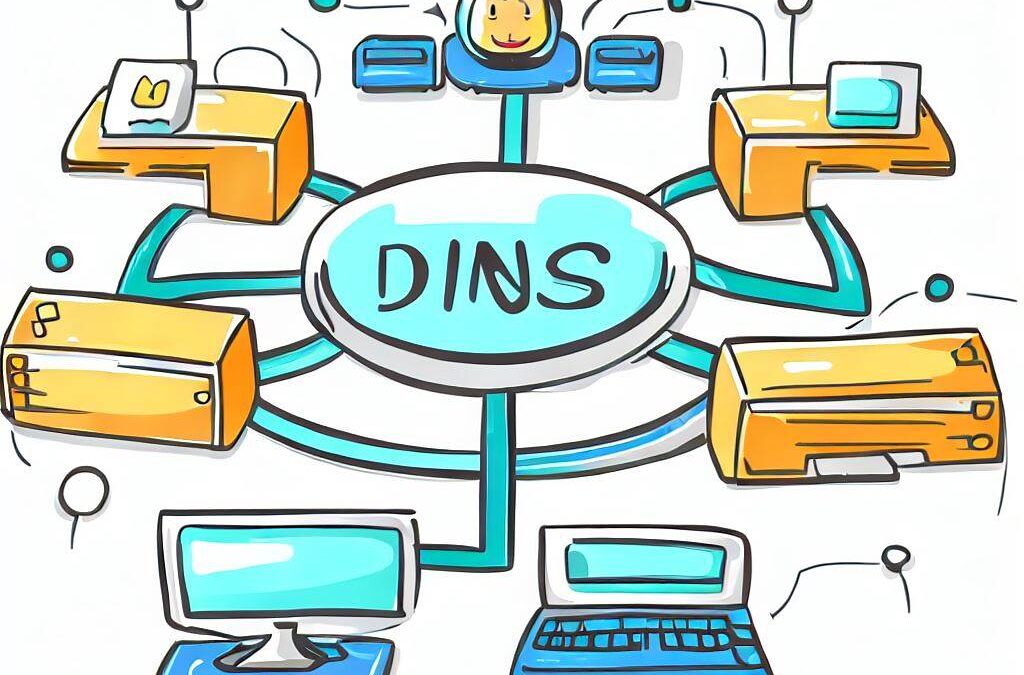
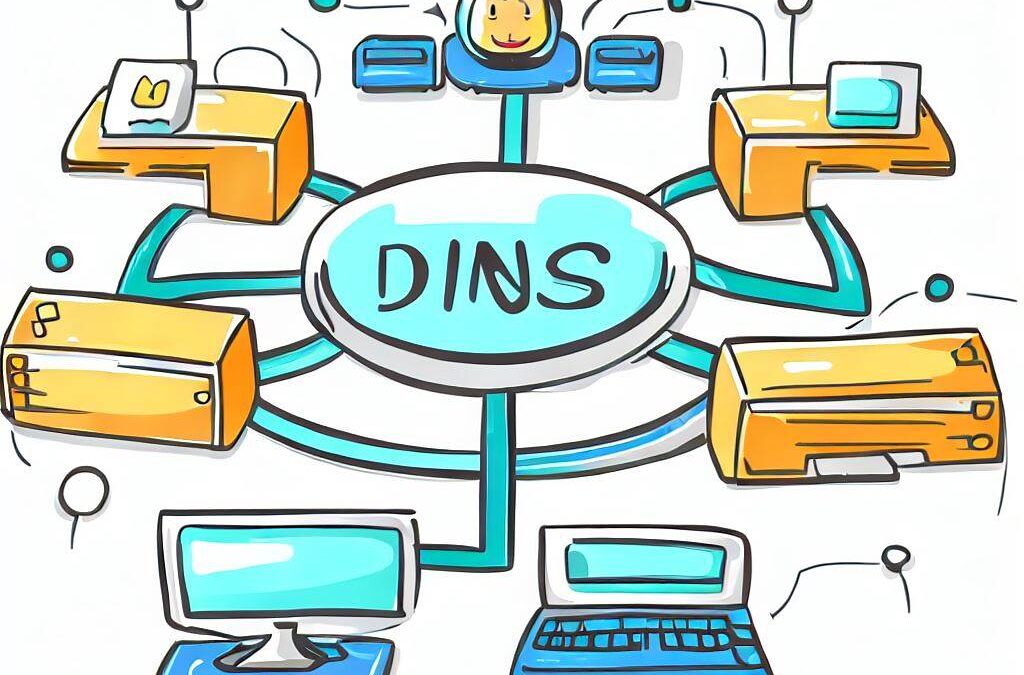
There are many reasons to limit the types of websites that are accessible from your work or home network. A couple of the most common are (1) to keep inappropriate material from being accessed, and (2) protect from known websites that serve malicious software or host...

by dlstrom-sds | Jun 13, 2023 | resources
An Introduction to Incident Response for SMBs Overview Every organization experiences cyberattacks and these are referred to as incidents. Incident almost always refers to something bad happening. Sometimes an incident results in a security breach. Breach is usually...
by dlstrom-sds | May 9, 2023 | resources
Multi-factor authentication (sometimes called two-factor authentication or two-step authentication) provides an extra layer of protection for your online accounts. It is like having multiple locks of different types of the door to your house. Usually we have a lock...





Recent Comments